How Can I Read the Results of Nmap When I Scan 1 Ip
Nmap is a network mapper that has emerged every bit one of the most pop, free network discovery tools on the market. Nmap is now ane of the cadre tools used by network administrators to map their networks. The program can exist used to find alive hosts on a network, perform port scanning, ping sweeps, Os detection, and version detection.
A number of recent cyberattacks accept re-focused attention on the type of network auditing that Nmap provides. Analysts take pointed out that the contempo Capital letter One hack, for instance, could have been detected sooner if organisation administrators had been monitoring connected devices. In this guide, nosotros'll wait at what Nmap is, what information technology can exercise, and explain how to use the most common commands.
Download the total Netcat cheatsheet
Ideally, Nmap should be used every bit office of an integrated Data Security Platform. Once Nmap has been used to map a network, a platform such as Varonis' Datadvantage tin can then exist used to implement advanced access control.
- How To Use Nmap
- Nmap Tutorial and Examples
- Nmap Commands
- Nmap FAQ
What is Nmap?
At its cadre, Nmap is a network scanning tool that uses IP packets to identify all the devices connected to a network and to provide information on the services and operating systems they are running.
The plan is nigh commonly used via a command-line interface (though GUI forepart-ends are too bachelor) and is bachelor for many different operating systems such every bit Linux, Costless BSD, and Gentoo. Its popularity has also been bolstered by an active and enthusiastic user back up community.
Nmap was developed for enterprise-scale networks and can scan through thousands of continued devices. Still, in recent years Nmap is beingness increasingly used by smaller companies. The ascent of the IoT, in particular, now means that the networks used by these companies have become more circuitous and therefore harder to secure.
This means that Nmap is now used in many website monitoring tools to audit the traffic between web servers and IoT devices. The recent emergence of IoT botnets, like Mirai, has too stimulated interest in Nmap, not least considering of its ability to interrogate devices connected via the UPnP protocol and to highlight whatever devices that may exist malicious.
What Does Nmap Practise?
At a practical level, Nmap is used to provide detailed, real-fourth dimension information on your networks, and on the devices continued to them.
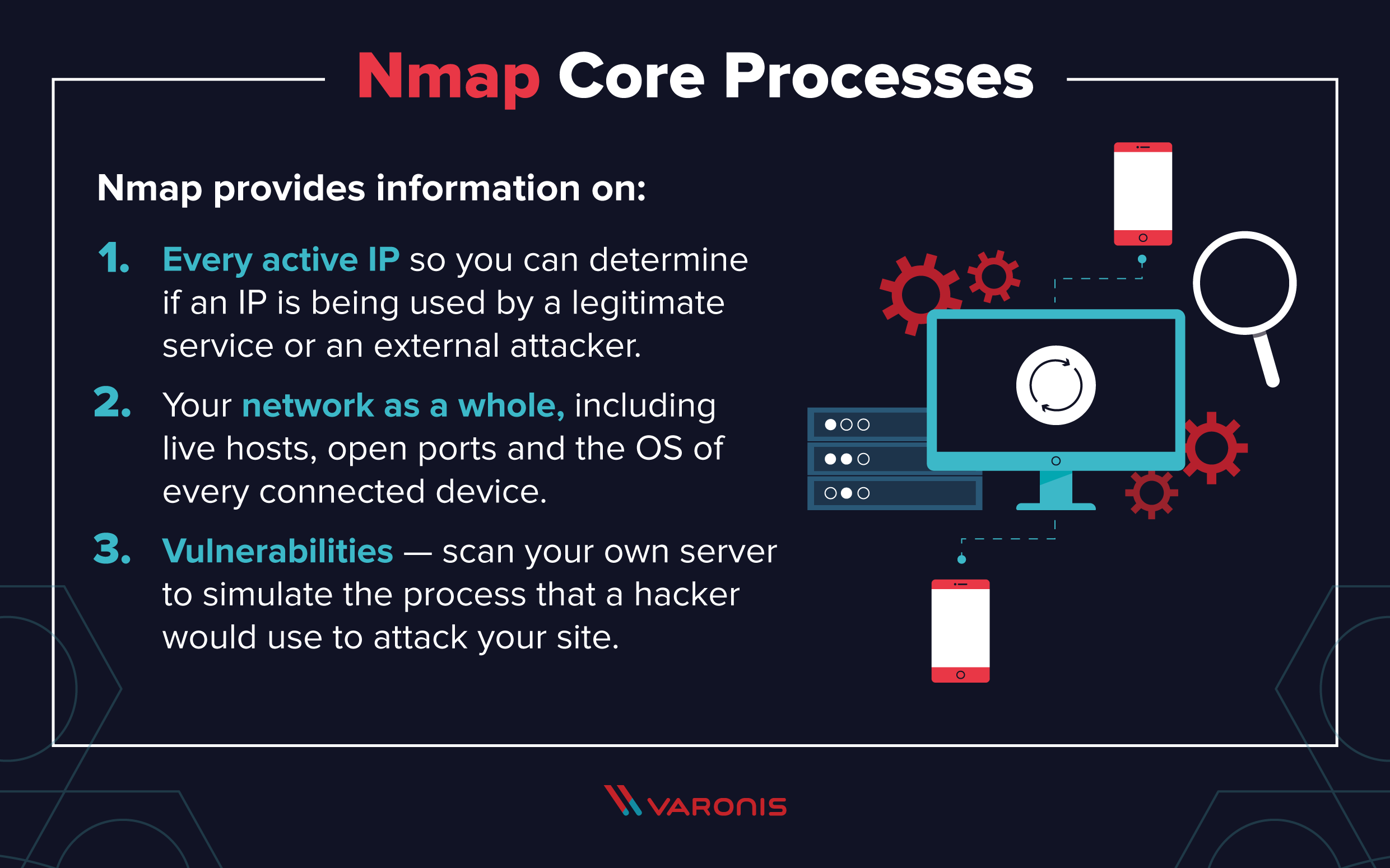
The primary uses of Nmap can be broken into three core processes. First, the program gives yous detailed data on every IP active on your networks, and each IP can then be scanned. This allows administrators to cheque whether an IP is being used past a legitimate service, or by an external aggressor.
Secondly, Nmap provides information on your network as a whole. It can be used to provide a list of alive hosts and open ports, as well as identifying the OS of every connected device. This makes information technology a valuable tool in ongoing system monitoring, as well as a critical part of pentesting. Nmap tin can be used aslope the Metasploit framework, for instance, to probe and and then repair network vulnerabilities.
Thirdly, Nmap has also become a valuable tool for users looking to protect personal and business websites. Using Nmap to browse your own web server, particularly if you are hosting your website from abode, is essentially simulating the process that a hacker would utilize to attack your site. "Attacking" your own site in this way is a powerful manner of identifying security vulnerabilities.
How To Use Nmap
Nmap is straightforward to employ, and near of the tools it provides are familiar to system admins from other programs. The reward of Nmap is that it brings a wide range of these tools into one plan, rather than forcing yous to skip between divide and discrete network monitoring tools.
In club to utilise Nmap, you need to exist familiar with command-line interfaces. Most avant-garde users are able to write scripts to automate common tasks, but this is non necessary for basic network monitoring.
How To Install Nmap
The process for installing Nmap is easy merely varies according to your operating arrangement. The Windows, Mac, and Linux versions of the program can exist downloaded here.
- For Windows, Nmap comes with a custom installer (namp<version>setup.exe). Download and run this installer, and it automatically configures Nmap on your system.
- On Mac, Nmap likewise comes with a dedicated installer. Run the Nmap-<version>mpkg file to offset this installer. On some recent versions of macOS, you might encounter a alert that Nmap is an "unidentified developer", but y'all can ignore this alarm.
- Linux users can either compile Nmap from source or use their called parcel manager. To use apt, for instance, you can run Nmap –version to check if Nmap is installed, and sudo apt-get install Nmap to install it.
Nmap Tutorial and Examples
Once you've installed Nmap, the all-time way of learning how to utilise it is to perform some basic network scans.
How To Run a Ping Scan
One of the almost basic functions of Nmap is to identify active hosts on your network. Nmap does this past using a ping scan. This identifies all of the IP addresses that are currently online without sending any packers to these hosts.
To run a ping scan, run the post-obit command:
# nmap -sp 192.100.i.1/24
This command and then returns a list of hosts on your network and the full number of assigned IP addresses. If you spot any hosts or IP addresses on this listing that you cannot account for, you tin so run further commands (see below) to investigate them farther.
How To Run A Host Browse
A more powerful way to scan your networks is to apply Nmap to perform a host scan. Unlike a ping scan, a host scan actively sends ARP request packets to all the hosts connected to your network. Each host then responds to this packet with another ARP bundle containing its status and MAC address.
To run a host scan, use the post-obit command:
# nmap -sp <target IP range>
This returns information on every host, their latency, their MAC accost, and as well any description associated with this address. This can exist a powerful mode of spotting suspicious hosts connected to your network.
If you see anything unusual in this list, you can so run a DNS query on a specific host, by using:
# namp -sL <IP address>
This returns a list of names associated with the scanned IP. This description provides information on what the IP is actually for.
How To Use Nmap in Kali Linux
Using Nmap in Kali Linux tin can be washed in an identical style to running the programme on any other flavor of Linux.
That said, there are advantages to using Kali when running Nmap scans. Most mod distros of Kali now come with a fully-features Nmap suite, which includes an advanced GUI and results viewer (Zenmap), a flexible data transfer, redirection, and debugging tool (Ncat), a utility for comparing scan results (Ndiff), and a packet generation and response analysis tool (Nping).
Nmap Commands
Well-nigh of the common functions of Nmap can be executed using a single control, and the program besides uses a number of 'shortcut' commands that can be used to automate common tasks.
Here is a quick run-downward:
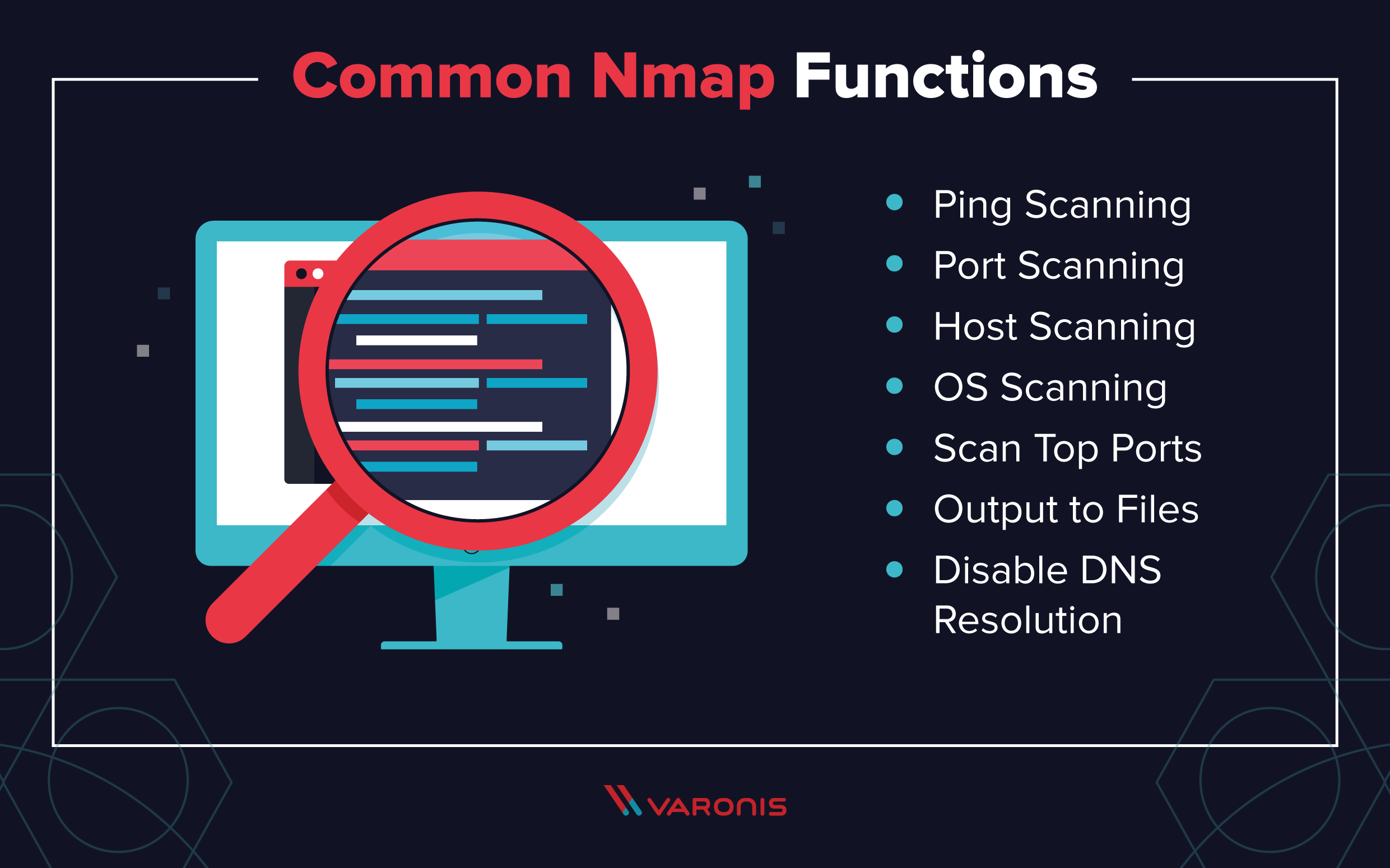
one. Ping Scanning
As mentioned to a higher place, a ping scan returns information on every active IP on your network. Yous can execute a ping scan using this command:
# nmap -sp 192.100.1.1/24
2. Port Scanning
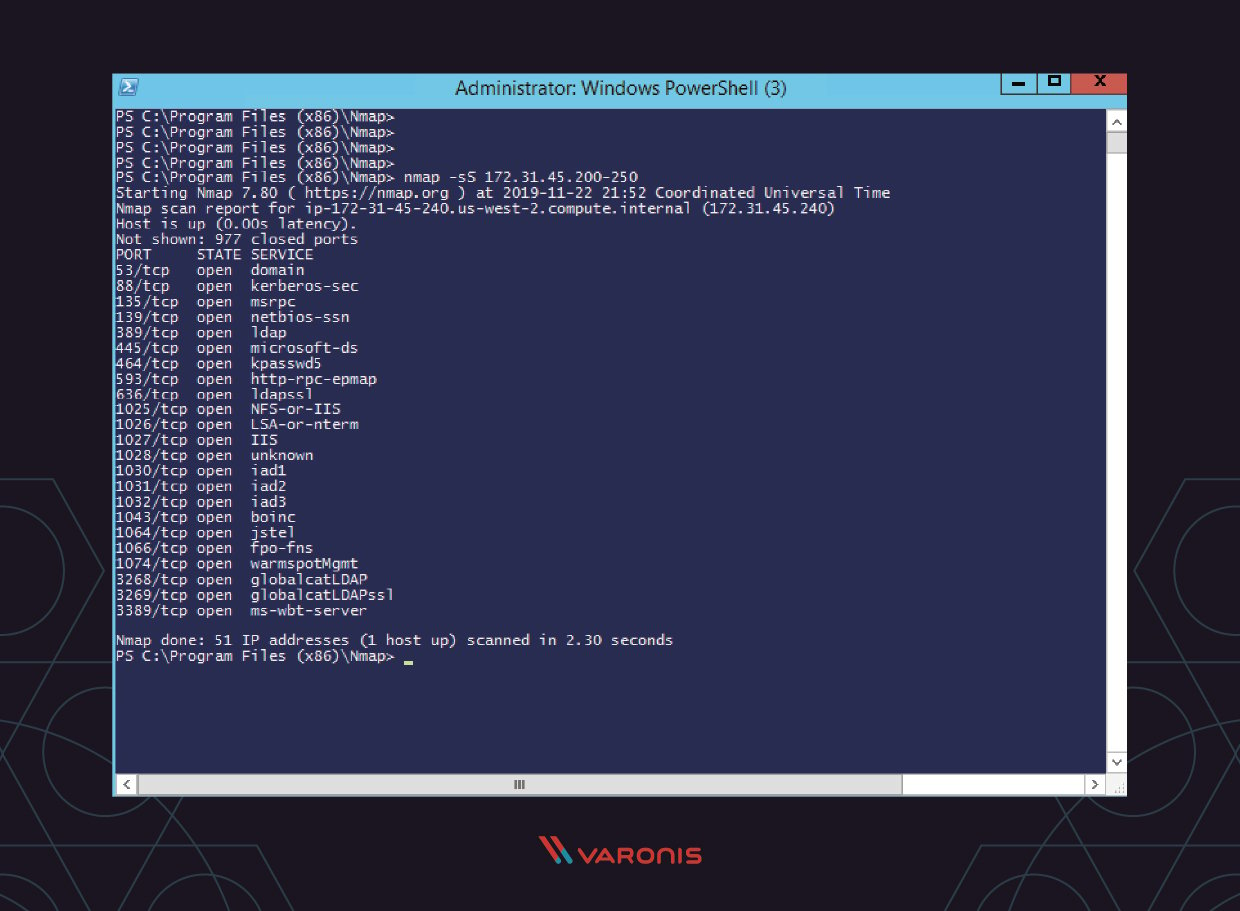
There are several means to execute port scanning using Nmap. The most commonly used are these:
# sS TCP SYN scan # sT TCP connect scan # sU UDP scans # sY SCTP INIT scan # sN TCP Zippo
The major differences between these types of scans are whether they comprehend TCP or UDP ports and whether they execute a TCP connectedness. Here are the basic differences:
- The most basic of these scans is the sS TCP SYN scan, and this gives almost users all the data they demand. Information technology scans thousands of ports per 2d, and because information technology doesn't complete a TCP connectedness it does not agitate suspicion.
- The main alternative to this type of scan is the TCP Connect scan, which actively queries each host, and requests a response. This type of scan takes longer than a SYN scan, simply tin can return more reliable information.
- The UDP scan works in a like fashion to the TCP connect browse but uses UDP packets to browse DNS, SNMP, and DHCP ports. These are the ports most oft targeted by hackers, and then this type of browse is a useful tool for checking for vulnerabilities.
- The SCTP INIT scan covers a dissimilar set of services: SS7 and SIGTRAN. This type of browse tin can also be used to avoid suspicion when scanning an external network because information technology doesn't complete the total SCTP process.
- The Elevation Aught scan is also a very crafty scanning technique. It uses a loophole in the TCP organization that tin reveal the status of ports without directly querying them, which ways that yous can run across their status even where they are protected by a firewall.
3. Host Scanning
Host scanning returns more detailed data on a item host or a range of IP addresses. As mentioned above, you can perform a host scan using the following command:
# nmap -sp <target IP range>
4. Os Scanning
Os scanning is ane of the well-nigh powerful features of Nmap. When using this type of scan, Nmap sends TCP and UDP packets to a item port, and and then clarify its response. It compares this response to a database of 2600 operating systems, and return information on the Bone (and version) of a host.
To run an Bone scan, employ the post-obit control:
# nmap -O <target IP>
5. Scan The Most Popular Ports
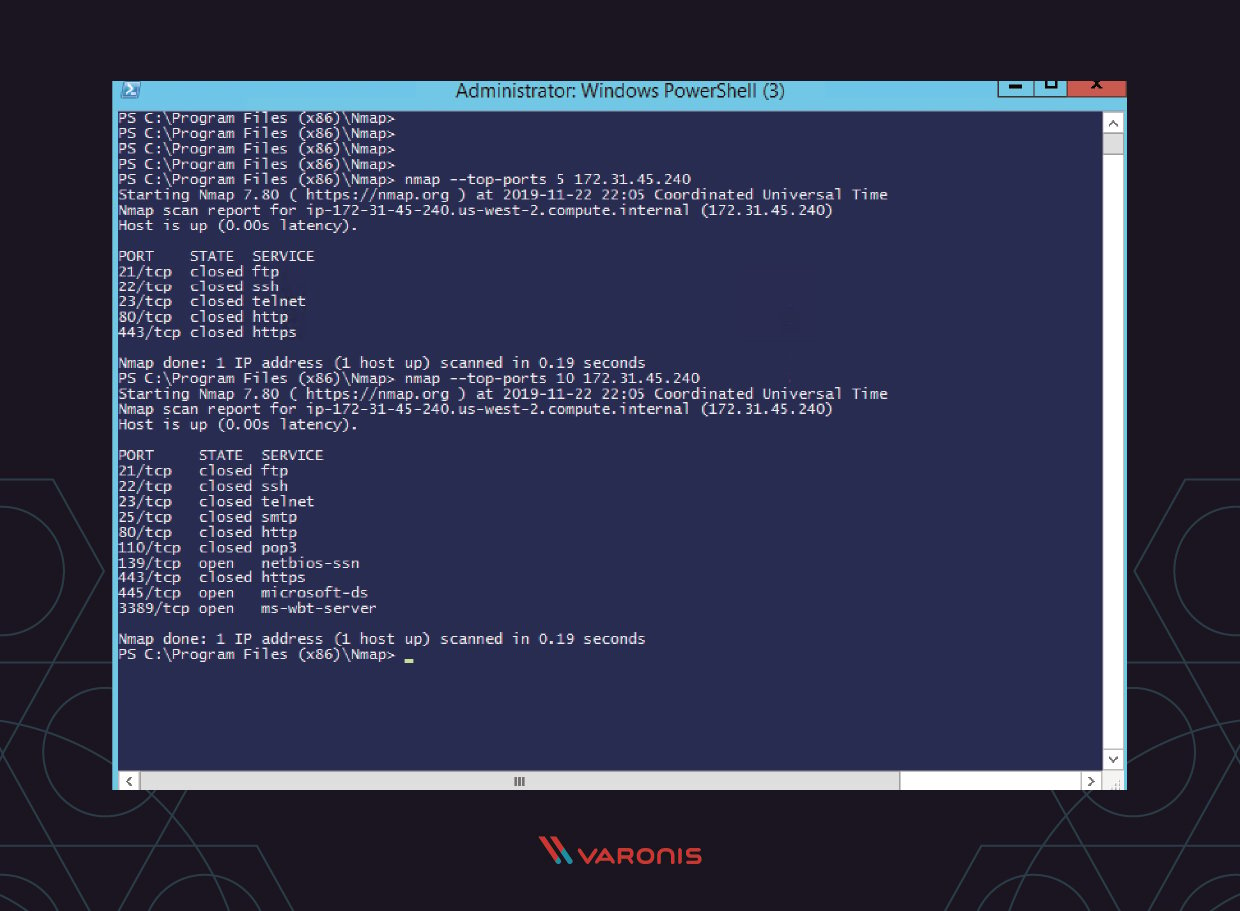
If you are running Nmap on a home server, this command is very useful. Information technology automatically scans a number of the most 'popular' ports for a host. You can run this control using:
nmap --elevation-ports xx 192.168.one.106
Replace the "20" with the number of ports to browse, and Nmap quickly scans that many ports. Information technology returns a concise output that details the status of the most common ports, and this lets you quickly see whether you take any unnecessarily open up ports.
6. Output to a File
If you want to output the results of your Nmap scans to a file, yous tin can add an extension to your commands to do that. Merely add together:
-oN output.txt
To your command to output the results to a text file, or:
-oX output.xml
To output to an XML.
7. Disable DNS Name Resolution
Finally, y'all tin can speed up your Nmap scans past using the -n parameter to disable reverse DNS resolution. This can exist extremely useful if y'all want to scan a big network. For example, to turn off DNS resolution for the basic ping scan mentioned above, add -n:
# nmap -sp -n 192.100.i.ane/24
Nmap FAQ
The commands above cover nigh of the basic functionality of Nmap. Yous might still accept some questions though, so let's run through the most common ones.
Q: What Are Some Nmap Alternatives?
There are some alternatives to Nmap, but most of them are focused on providing specific, niche functionality that the boilerplate system administrator does need frequently. MASSCAN, for instance, is much faster than Nmap but provides less detail. Umit, by contrast, allows you lot to run several scans at once.
In reality, however, Nmap provides all the functionality and speed that the average user requires, especially when used alongside other similarly popular tools like NetCat (which tin can be used to manage and control network traffic) and ZenMap (which provides a GUI for Nmap)
Q: How Does Nmap Work?
Nmap builds on previous network auditing tools to provide quick, detailed scans of network traffic. Information technology works past using IP packets to identify the hosts and IPs active on a network and so analyze these packets to provide information on each host and IP, equally well every bit the operating systems they are running.
Q: Is Nmap Legal?
Aye. If used properly, Nmap helps protect your network from hackers, considering information technology allows you to quickly spot whatsoever security vulnerabilities in your systems.
Whether port scanning on external servers is legal is another issue. The legislation in this area is circuitous and varies past territory. Using Nmap to scan external ports can lead to yous being banned by your ISP, and then brand sure you inquiry the legal implications of using the program before you start using information technology more than widely.
The Bottom Line
Taking the time to learn Nmap can dramatically increase the security of your networks because the program offers a quick, efficient mode of auditing your systems. Even the bones features offered past the program – such as the ability to perform port scanning – rapidly reveal any suspicious devices that are active on your network.
Using Nmap to perform frequent network audits tin can aid you avert condign easy prey for hackers, whilst also improving your knowledge of your ain network. In addition, Nmap provides functionality that complements more fully-featured data security platforms such as that offered by Varonis, and when used alongside these tools tin can dramatically meliorate your cybersecurity.
Source: https://www.varonis.com/blog/nmap-commands
0 Response to "How Can I Read the Results of Nmap When I Scan 1 Ip"
Enregistrer un commentaire